
LLM SATs FTW
Practical experiments using LLMs for Structured Analytic Techniques in threat intelligence analysis.

Practical experiments using LLMs for Structured Analytic Techniques in threat intelligence analysis.
Essential tagging patterns and best practices for Synapse threat intelligence platform workflows.
Like everyone else I’ve been following the tragic war in Ukraine and mourning the loss of life and humanitarian crisis. Professionally as an analyst in the threat intelligence and computer network defense world I’ve been considering what this war and spillover means for defending networks, especially as organizations like CISA keep putting out bulletins regarding threats of Russian nexus adversaries.
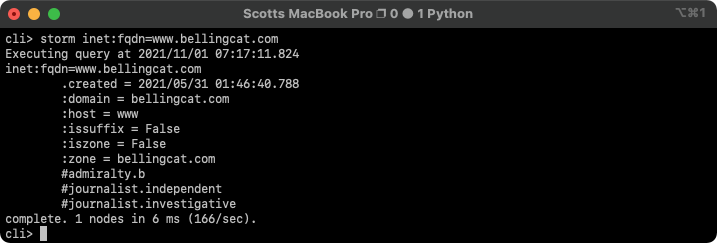
Complete beginner guide to installing and using Synapse threat intelligence platform with practical examples.

Analysis of threat intelligence sharing challenges using culinary metaphors and community dynamics.
The APT hype cycle: how threat groups go from feared to dismissed. Why both over and underestimating adversaries is dangerous.
A few weeks ago while teaching SANS FOR578 one of my students asked a great question by a student: What books or papers should a new cyber threat i…

U.S. government response to Russian election interference: sanctions, IOCs, and diplomatic actions against Grizzly Steppe.
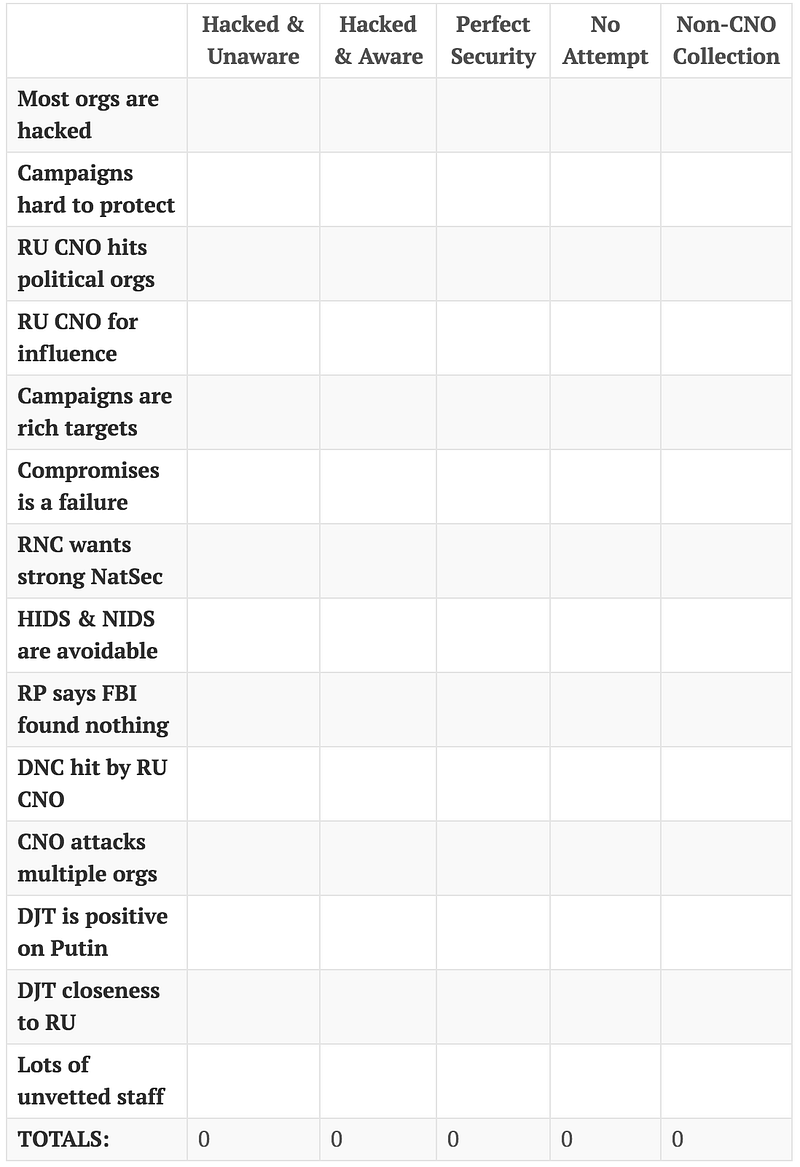
This post gets political. People may agree or disagree based on their own experience or personal belief.

Strategic framework for prioritizing threat intelligence collection from internal data to commercial feeds.