pbcopy and pbpaste
Master macOS clipboard manipulation from terminal with pbcopy and pbpaste for productivity workflows.
Master macOS clipboard manipulation from terminal with pbcopy and pbpaste for productivity workflows.
Confronts impostor syndrome in DFIR with real experiences and actionable advice for overcoming self-doubt.
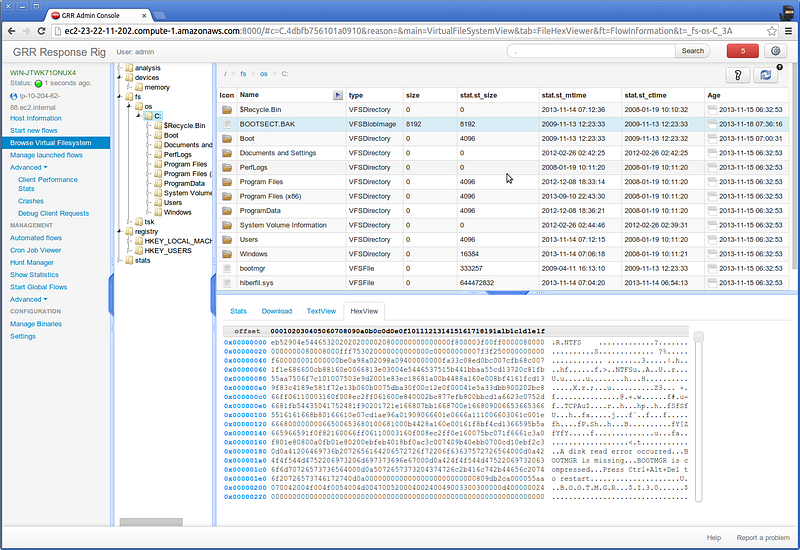
Key open source tools that enable proactive threat hunting including osquery, ELK, and Moloch.

Talk to anyone in the DFIR Illuminati and one of the topics that always comes up is Hunting.
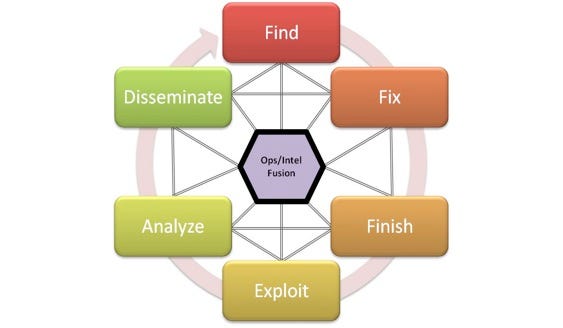
F3EAD methodology: combining military operations with intelligence cycles for effective incident response.
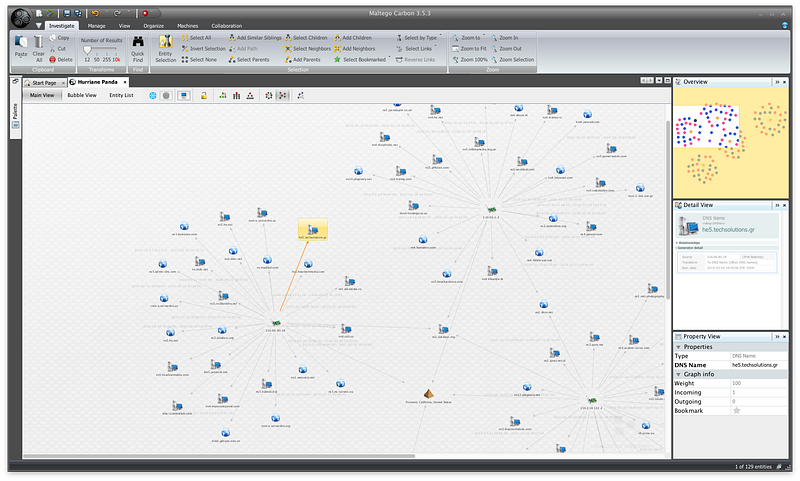
Step-by-step guide to building custom Maltego transforms with Python examples and automation tips.
A small number of topics get intelligence driven incident responders incredibly frustrated. Using intelligence to mean smart (I’ll share more about that later this week).
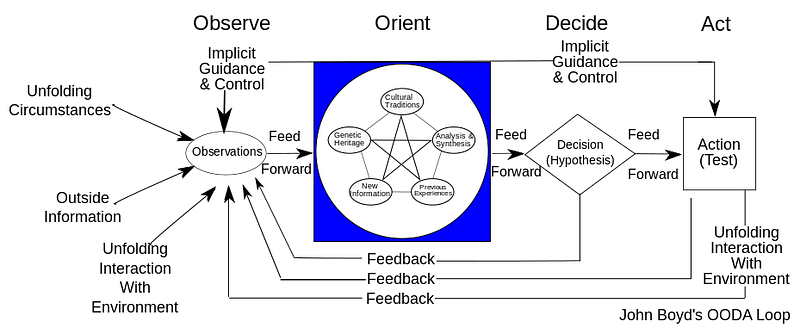
Understanding the OODA Loop for faster incident response and security decision-making cycles.
The challenges of cybersecurity attribution: incomplete data, easy spoofing, and avoiding bias in threat analysis.
Practical guide to mastering Git and GitHub with curated learning resources and workflow tips from a security expert.